
Exchange Architecture and Custody Models in Crypto Trading
Crypto exchanges operate across a spectrum of custody, order matching, and settlement models. Choosing the right…
0 articles

Crypto exchanges operate across a spectrum of custody, order matching, and settlement models. Choosing the right…
Forecasting Ethereum’s 2024 performance requires separating signal from narrative. This article builds a technical framework around…
Canadian traders face a distinct set of technical and regulatory constraints when selecting a crypto exchange.…
Regulatory frameworks for crypto and defi continue to fragment across jurisdictions, creating a patchwork of compliance…

When a cryptocurrency exchange pursues a traditional equity initial public offering, it converts a privately held…

Crypto markets generate thousands of news items daily across protocol upgrades, exploit disclosures, regulatory filings, token…

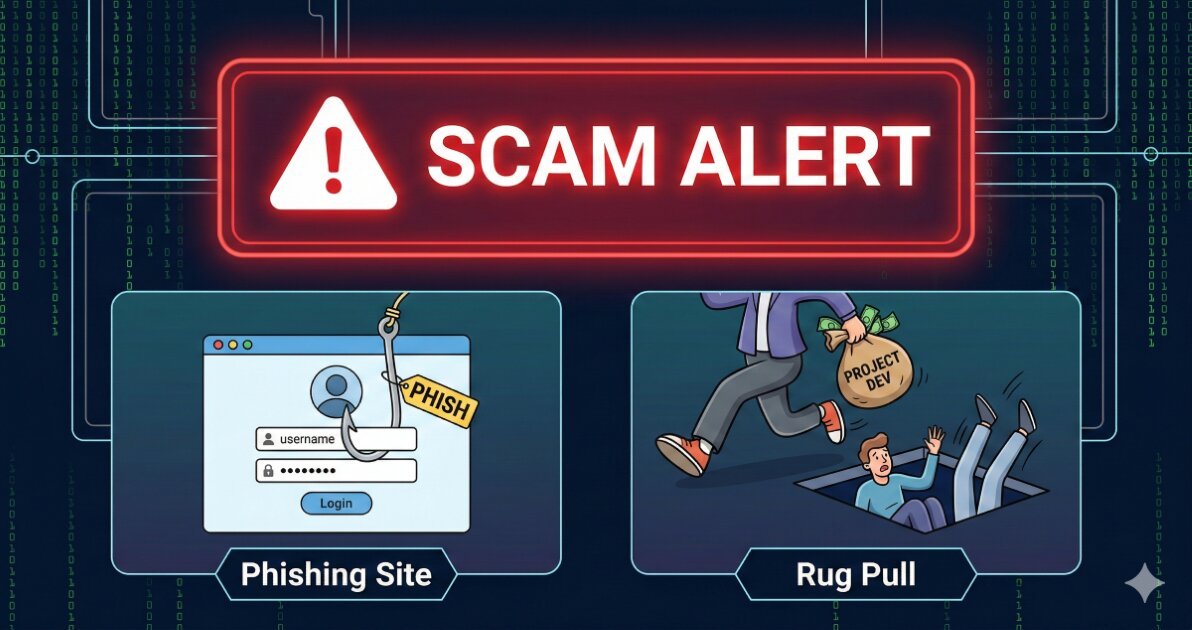
PancakeSwap operates as an automated market maker (AMM) on BNB Chain and other networks, offering decentralized…

Bitcoin price forecasting combines quantitative models, onchain analytics, and market microstructure analysis to estimate future price…
Crypto exchange regulation exists on a spectrum that runs from comprehensive licensing regimes to functional prohibition.…
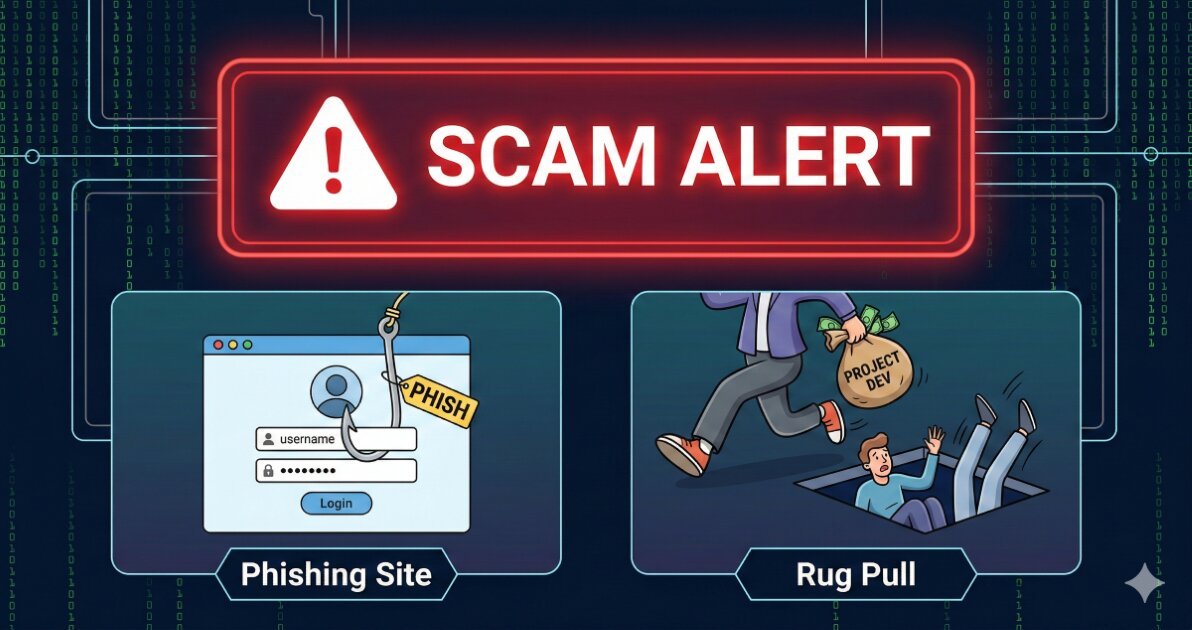
Crypto security failures cascade from discrete implementation choices, not abstract negligence. Whether you manage protocol treasury…